QUICKLOOK: What a Nation State Exploit looks like: Unraveling Operation Triangulation
A Zero-Click Sophisticated iOS Zero-Day Exploit Chain
Silent Strike: Anatomy of an iOS Zero-Day Attack
Abstract:
Operation Triangulation represents a highly intricate and advanced cyber-espionage campaign meticulously designed to target Apple iOS devices. This campaign relies on a series of zero-day vulnerabilities to circumvent Apple's robust hardware-based security mechanisms, presenting a significant challenge to user privacy and data security. This article provides an exhaustive technical analysis of the attack methodology, the precise vulnerabilities leveraged, and the wider implications for the realm of cybersecurity. The revelation of Operation Triangulation underscores the ongoing imperative for relentless vigilance and the continual evolution of security measures in response to ever-evolving and increasingly sophisticated cyber threats.
Introduction:
Cybersecurity firm Kaspersky has identified an obscure hardware feature in iPhones that was exploited by hackers in a campaign dubbed "Operation Triangulation." The exploit involves bypassing hardware-based security to attack iPhones via iMessages with malicious attachments. This advanced technique marks one of the most sophisticated attack chains uncovered to date, raising concerns about even the most robust hardware-based protections.
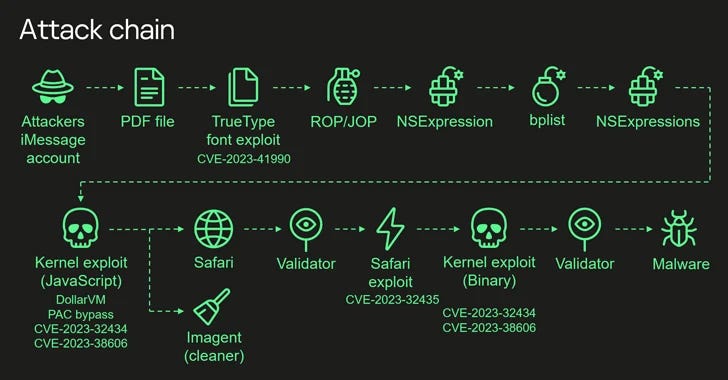
This multifaceted exploit chain represents a new pinnacle of cyber attack sophistication on personal devices, highlighting the lengths to which attackers go to compromise systems. Starting from an undocumented TrueType font instruction, the exploit cleverly navigates through a series of vulnerabilities and techniques, including return/jump-oriented programming, JavaScript obfuscation, memory manipulation, and hardware-based bypasses. The comprehensive nature of these exploits — from the initial message reception to the final spyware payload execution — underscores the critical need for robust, multi-layered cybersecurity measures and the constant vigilance required in both software and hardware domains.
Findings:
This campaign utilized a zero-day exploit chain to compromise iOS devices and steal sensitive information. The attack, which first emerged in June 2023, exploited security flaws in iOS, including CVE-2023-32434 and CVE-2023-32435, through a zero-click exploit delivered via iMessage.
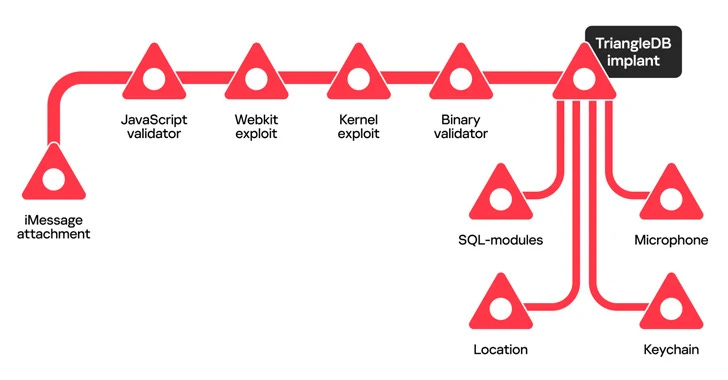
TriangleDB Implant: The Heart of the Attack:
A multifaceted implant, with several modules designed to compromise the victim's device comprehensively:
Recording Microphone: One module had the capability to record audio from the device's microphone, essentially eavesdropping on conversations and ambient sounds.
Extracting iCloud Keychain: Another module targeted the iCloud Keychain, extracting sensitive information, including passwords and credentials.
Stealing Data from SQLite Databases: TriangleDB could steal data from SQLite databases used by various apps on the device, potentially compromising messages, contacts, and other critical data.
Estimating Victim's Location: The implant's ability to estimate the victim's location was particularly intriguing. It accomplished this by utilizing GSM data, including the mobile country code (MCC), mobile network code (MNC), and location area code (LAC). This allowed the attacker to triangulate the approximate location of the compromised device, even when GPS data was unavailable.
Stealth and Persistence
Operation Triangulation went to great lengths to remain covert. The microphone-recording module had a built-in mechanism to suspend recording when the device's screen was active or when the battery level dropped below 10%. This tactical approach aimed to fly under the radar and avoid detection.
TriangleDB maintained communication with a command-and-control (C2) server, ensuring the attacker's control over the compromised device. The server could issue commands to the implant, further enhancing its capabilities.
What the C2 looked like:
The operation aimed to infect iOS devices with the TriangleDB implant while maintaining a low profile to avoid detection. To achieve this, they employed a series of validation components, including JavaScript and Binary Validators, to assess the target device's suitability for implantation.
Giving credence to this actor being a intelligence service the attackers employed several modules to steal sensitive data from infected devices. These modules included a microphone recording module, keychain exfiltration, SQLite stealing modules, and a location-monitoring module. These actions allowed them to collect a wide range of data, from audio recordings to user information and installed applications.
The attackers also exhibited a deep understanding of iOS internals, using private and undocumented APIs in their attack. Furthermore, they targeted both iOS and macOS systems, suggesting a broader scope for their campaign.
Operation Triangulation Attack Chain: A Rough Breakdown
Operation Triangulation, a highly sophisticated cyberattack campaign targeting Apple iOS devices, involved a meticulously planned attack chain. In this article, we will provide a comprehensive breakdown of the steps and stages that attackers employed to compromise these devices.
Stage 1: The Zero-Click Exploit
The attack began with a zero-click exploit, meaning no user interaction was required. Victims received an iMessage with a malicious attachment. This attachment initiated the attack chain, aiming to gain elevated permissions and deploy a spyware module.
CVE-2023-41990 - FontParser Flaw
Assessment: Attackers exploited a vulnerability in the FontParser component. It allowed them to execute arbitrary code using a maliciously crafted font file, often sent via iMessage.
Stage 2: Exploiting Kernel Vulnerabilities
CVE-2023-32434 - Kernel Integer Overflow
Assessment: This vulnerability enabled malicious apps to execute arbitrary code with kernel privileges. It was part of the chain used to escalate privileges.
CVE-2023-32435 - WebKit Memory Corruption
Assessment: Attackers leveraged this memory corruption issue in WebKit, enabling arbitrary code execution when processing specially crafted web content. It further facilitated privilege escalation.
Stage 3: Bypassing Hardware-Based Security
CVE-2023-38606 - Kernel State Modification
Assessment: CVE-2023-38606 allowed malicious apps to modify sensitive kernel state, bypassing hardware-based security protections. This critical step granted attackers total control over compromised systems.
Stage 4: Surveillance and Data Exfiltration
After gaining control, the attackers initiated surveillance and data exfiltration.
Microphone Recording: The spyware module could record audio from the device's microphone. Importantly, it was programmed to suspend recording when the device's screen was turned on or if the battery level was below 10%, enabling covert operation.
Location Tracking: The spyware utilized GSM data, including mobile country code (MCC), mobile network code (MNC), and location area code (LAC), to triangulate the victim's location when GPS data was unavailable.
Stage 5: Covering Tracks
The attackers took steps to cover their tracks and evade detection.
Deleting Evidence: They removed crash logs and deleted traces of the malicious iMessage attachment sent from various attacker-controlled email addresses.
Checking Jailbreak Status: The spyware checked whether the target device was jailbroken.
Personalized Ad Tracking: It enabled personalized ad tracking.
Gathering Device Information: Information such as the device's username, phone number, IMEI, and Apple ID was collected.
App Enumeration: A list of installed apps was retrieved.
Now what?
Operation Triangulation raises significant concerns regarding personal security, especially for individuals who use Apple iOS devices. The campaign's ability to compromise iPhones through sophisticated techniques serves as a wake-up call for users to be more vigilant about their digital security.
User Awareness: This incident underscores the importance of user awareness and education. Many cyberattacks, including this one, rely on unsuspecting users to execute malicious code unwittingly. Users should be cautious when receiving unexpected messages or attachments and avoid clicking on suspicious links or downloading files from unknown sources.
Software Updates: Keeping your iOS device updated with the latest security patches and software updates is crucial. Manufacturers regularly release updates to address vulnerabilities, and users must ensure their devices are running the most current software to mitigate potential threats.
App Permissions: Reviewing app permissions is essential. Users should scrutinize the permissions granted to apps and restrict unnecessary access to personal information, location data, and device features, such as the microphone and camera.
Password Management: Robust password management practices are indispensable. Employ strong, unique passwords for online accounts and enable two-factor authentication wherever possible to add an extra layer of security.
Security Software: Consider installing reputable security software on your iOS device. While iOS is known for its robust security, third-party security apps can provide additional protection against emerging threats.
Github resources:
Triangle Check: scan iTunes backups for traces of compromise by Operation Triangulation
triangleDB_unmunge_strings: A very simple python script that lets you "unmunge" hex strings from TriangleDB iOS spyware
Closing Thoughts:
The revelations surrounding Operation Triangulation paint a vivid picture of the ever-changing landscape of cybersecurity threats. What stands out most is the audacious use of zero-day vulnerabilities and a highly advanced implant to compromise iOS devices.
In terms of personal security, this incident should prompt us to reevaluate our online habits and take our digital safety more seriously. While the campaign primarily targeted iOS devices, it's a stark reminder that no platform is entirely immune to such attacks. This means that whether you're using iOS or any other system, it's crucial to stay vigilant and adopt strong security practices to protect your personal information.
Media organizations and prominent individuals should take particular note of Operation Triangulation. It highlights the fact that determined attackers are willing to go to great lengths to target specific individuals or groups through cyber espionage. Media figures, journalists, and public personalities often find themselves in the crosshairs due to their influence and access to sensitive information. As a result, it's imperative for them to not only focus on physical security but also invest in robust digital defenses and cybersecurity training.